Maximize Performance with Universal Cloud Storage Service and Assistance
Wiki Article
Enhance Information Security With Universal Cloud Storage
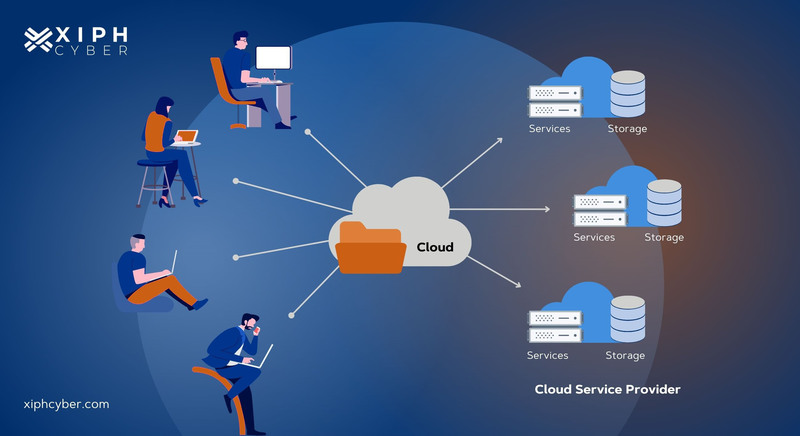
In today's digital landscape, the demand to protect data has come to be paramount for companies of all dimensions. Universal cloud storage space uses a compelling option to reinforce information safety procedures through its durable attributes and capabilities. By utilizing the power of file encryption, gain access to controls, and disaster healing techniques, universal cloud storage not only safeguards delicate details however additionally ensures data availability and honesty. The inquiry continues to be: just how can companies efficiently take advantage of these devices to strengthen their data security posture and remain in advance in an ever-evolving hazard landscape?Advantages of Universal Cloud Storage Space
Exploring the advantages of carrying out Universal Cloud Storage space discloses its effectiveness in boosting data protection procedures. One of the vital benefits of Universal Cloud Storage space is its capacity to offer a central and safe platform for storing data. This central strategy enables simpler gain access to and monitoring of information, resulting in raised efficiency in information dealing with procedures. In Addition, Universal Cloud Storage space uses scalability, permitting services to easily broaden their storage capacity as their data needs expand, without the requirement for considerable investments in framework.Additionally, Universal Cloud Storage boosts data safety and security with attributes such as file encryption, access controls, and automated back-ups. Automated back-ups ensure that information is frequently backed up, lowering the danger of information loss due to mishaps or cyber strikes.
Trick Attributes for Information Protection
Trick protection attributes play an essential duty in protecting data honesty and discretion within Universal Cloud Storage systems. Furthermore, regular information back-ups are crucial for stopping data loss due to unexpected events like system failures or cyber-attacks.Verification devices such as multi-factor authentication and strong password needs add an added layer of security by confirming the identity of individuals accessing the cloud storage space. Intrusion discovery and avoidance systems constantly monitor for any kind of questionable activities and aid mitigate prospective protection breaches. Furthermore, audit logs and task monitoring make it possible for organizations to track information accessibility and modifications, aiding in the discovery of any unapproved activities. In general, these vital attributes collectively add to robust data defense within Universal Cloud Storage systems.
Applying Secure Accessibility Controls
Safe accessibility controls are pivotal in ensuring the integrity and discretion of information within Universal Cloud Storage systems. By applying safe accessibility controls, organizations can regulate who can see, customize, or delete data kept in the cloud. One essential element of safe gain access to controls is authentication. This process verifies the identification of users attempting to access the cloud storage system, preventing unapproved individuals from obtaining entry.Another vital element is permission, which establishes the degree of access given to authenticated users. Role-based access control (RBAC) is an usual method that appoints specific authorizations based on the duties people have within the organization. my response Furthermore, carrying out multi-factor authentication adds an additional layer of safety by requiring users to offer numerous kinds of confirmation prior to accessing information.
Routine monitoring and auditing of gain access to controls are important to find any suspicious tasks without delay. By constantly reviewing and fine-tuning access control policies, organizations can proactively safeguard their information from unapproved accessibility or violations within Universal Cloud Storage settings.
Information Security Best Practices
Data security finest practices entail encrypting information both in transportation and at remainder. When information is in transportation, using safe and secure communication protocols such as SSL/TLS makes certain that info traded between the user and the cloud storage is encrypted, protecting against unauthorized access.Key monitoring is another important my review here aspect of information encryption ideal methods. Carrying out appropriate key management procedures makes certain that security tricks are securely stored and handled, avoiding unauthorized access to the encrypted data. Regularly updating security secrets and rotating them aids boost the security of the data gradually.
Backup and Calamity Healing Approaches
To ensure the connection of operations and protect against data loss, organizations have to develop robust backup and disaster recovery approaches within their Universal Cloud Storage systems. In the occasion of information corruption, unintended deletion, or a cyber attack, having reputable back-ups is necessary for bring back lost details swiftly. Back-up approaches need to consist of routine automatic back-ups of crucial data to multiple areas within the cloud to mitigate the danger of data loss. It is a good idea to implement a mix of full backups and step-by-step back-ups to maximize storage area and reduce healing time. Calamity recovery strategies should outline treatments for bring back information and applications in case of a disastrous event that impacts the key cloud storage. Testing these strategies periodically is crucial to guarantee why not look here their performance and recognize any type of potential gaps in the recovery procedure. By applying comprehensive back-up and calamity healing methods, organizations can improve the strength of their information monitoring techniques and minimize the effect of unforeseen information events.Conclusion
In conclusion, global cloud storage provides a robust solution for enhancing data safety and security with attributes like security, gain access to controls, and back-up approaches. By carrying out protected access controls and following information security best practices, companies can properly protect delicate information from unauthorized accessibility and protect against information loss. Backup and calamity recovery approaches further enhance data protection measures, guaranteeing data stability and accessibility in case of unforeseen events.Report this wiki page